-
- 05 Sep
Why I Trust — and Double-Check — Every Phantom-Like Wallet I Install
Okay, so check this out—I’ve been messing with Solana wallets for years. Wow! My first instinct was just to grab whatever extension popped up in a search, but that’s a bad habit. Initially I thought all browser wallet extensions behaved roughly the same, but then I watched one freeze a trade and nearly lose a fee, so that changed my view. On one hand convenience is king; on the other hand, security is the bouncer you can’t bribe.
Here’s the thing. Seriously? Using a browser extension wallet feels like leaving your bike locked in front of a coffee shop. Short-term it’s fine. Long-term, you want a U-lock and a camera. My instinct said «keep keys offline,» though actually, wait—I’ve also needed quick access to mint an NFT at 2 AM, so trade-offs exist. I’m biased, but I prefer wallets that make the trade-offs visible, not hidden.
When I evaluate a Solana extension wallet (yeah, I’m talkin’ Phantom-like tools), I look at three things first: provenance, permission behavior, and signature transparency. Hmm… those are boring words but they matter. Provenance means who made the extension and whether the code or the team is traceable; permission behavior is how chatty the extension is with sites; signature transparency is whether the wallet clearly shows what you’re signing. Initially I thought a slick UI was enough, but then I saw a permission dialog that asked for full access to a whole dApp collection and that felt off.
One practical pattern I follow: never use an extension from a random search result. Really? Yes. Instead, go to the project’s official site or a trusted mirror and follow their link. When in doubt, community channels and verified GitHub repos help. There are legit downloads and then there are lookalikes that are very convincing—some are almost photorealistic copies. (Oh, and by the way… phishers will often use small domain differences like «.app» vs «.io» to bait you.)
For US users I lean on familiar trust signals—verified Twitter accounts (yeah, I know…), published audits, and well-known ecosystem partners. Wow! It’s not foolproof. On balance these signals tilt the risk lower though not to zero. I run through a checklist before I click «Install»: developer history, store reviews (read the negative ones), and open-source status if available. I’m not 100% sure any one signal is decisive, but the combined pattern gives me a gut sense that something’s genuine.
How to spot a sketchy Phantom-style extension
Wow! First look at the store listing and developer name. Short titles and lots of hype are red flags. Then check the permissions the extension requests—are they asking to read all websites or only to connect to Solana sites? My instinct said «if they ask for more than needed, back out.» On a more analytical level, compare the extension ID or publisher page to the official project’s links; legitimate projects usually link back to the exact store entry.
Here’s the link I trust for a vetted download sometimes when I’m helping friends: https://sites.google.com/cryptowalletextensionus.com/phantomwalletdownloadextension/ . Really, that’s where I started when I needed a quick reminder of official sources. Initially I thought pinning a single source was too rigid, but then I realized having one known-good anchor can save you from a lot of scamming. On the other hand, always cross-check—don’t rely on a single place forever.
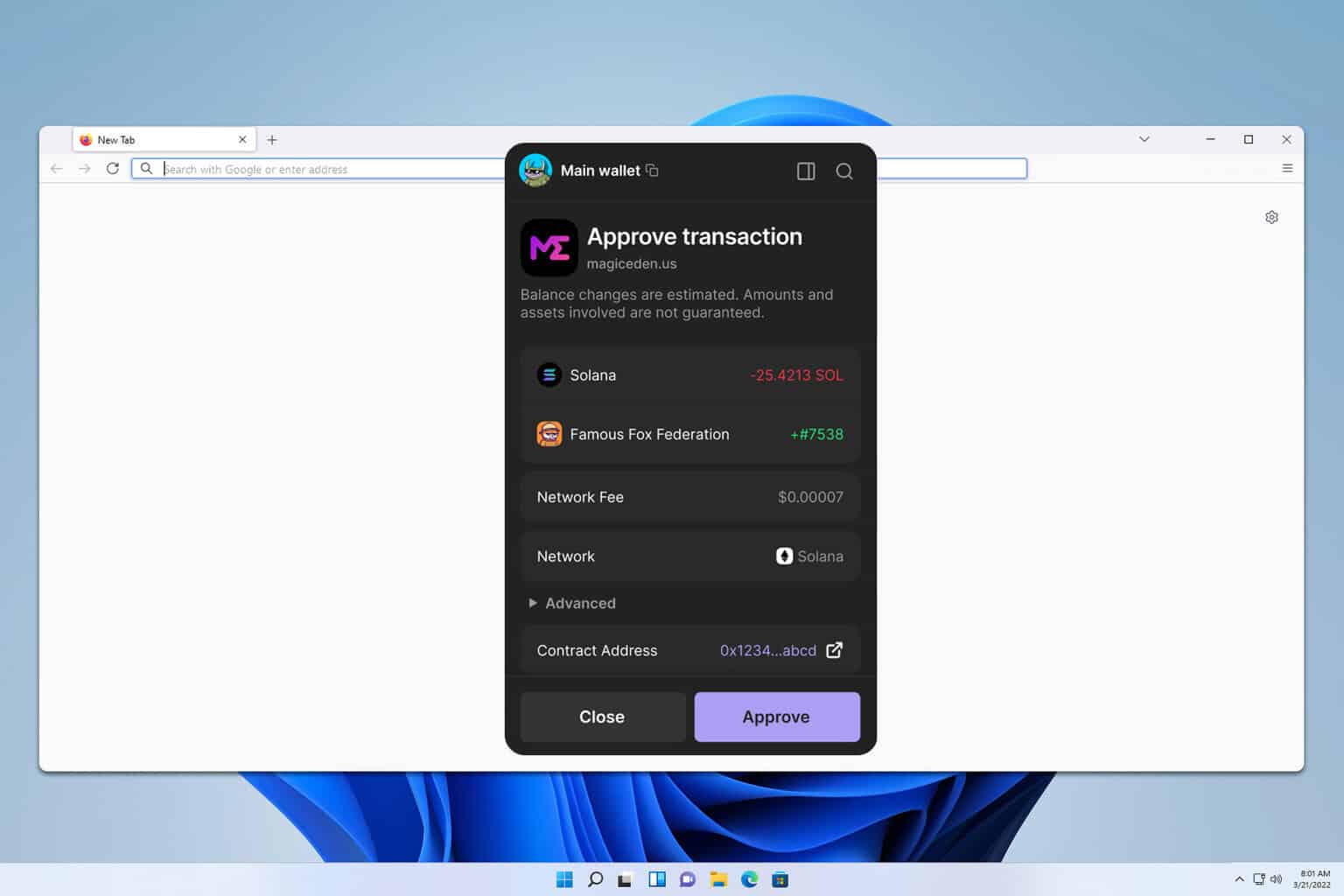
Don’t ignore the finer UX cues. Longer sentences in permission pop-ups that obfuscate what you’re signing are suspicious. Watch for vague language like «allow access to your data» without clarifying which data. My experience: clear, concise dialogs that show exact transaction details are friendlier and safer. Something felt off about extensions that try to rush a connection; they often include countdowns or urgent prompts—classic social-engineering moves.
Okay, let’s be honest—nobody wants to read a legal doc when they’re minting an NFT at midnight. I’m guilty too. But skim the key parts. Short, direct confirmations beat tiny checkboxes buried in walls of text. On the flip side, if a wallet shows exactly what you’re about to sign (token IDs, recipient addresses, fee), that’s a sign the designers understand user safety. I love clean UX, but not at the expense of hiding details.
I’ll share a routine I use. Short list: use a hardware wallet for large balances; use a browser extension for daily moves; keep a burner wallet for risky mints or airdrops. It sounds obvious, but people skip the basics. Initially I thought a single-wallet-for-everything setup was fine, but then I had to explain to a friend why his rare NFT was suddenly listed for sale without his approval—yeah, it sucks. On reflection, compartmentalization buys you peace of mind.
Some technical things to check if you want to be nerdy about it: look for content hashes on store pages, compare extension IDs, and if you’re brave, verify signatures against the project’s repo. Hmm… these steps are not for everyone, though they’re doable for power users. I’ve walked through this with a few colleagues; the process is tedious but comforting. If you don’t want to do that, at least follow community feedback and audit reports.
Here’s what bugs me about the current ecosystem: wallets sometimes act like black boxes. Seriously? Transactions emerge and the user is told «trust us»—no thanks. The industry has to do better at explaining what a signature does in plain English. That said, I’ve seen improvements year over year; UX teams in the Solana space are getting more serious about transparency, and that trend helps.
On the topic of NFTs specifically, minting flows can be a minefield. Short attacks include fake collection pages that trick wallets into approving sweeping permissions. Long attacks are more subtle and might involve compromised metadata servers that change an image after minting. Initially I underestimated metadata risk, but then a changelog switch made a minted piece point to a different image. Now I check contract activity and metadata endpoints when I’m targeting expensive mints.
Practice good habits. Keep your seed phrase offline and never copy it into a browser field. Really? Yes. Treat your seed like cash in a physical safe. A small tip: write it down twice and store each copy separately. I’m not saying paranoia, but a little redundancy saves heartbreak. If you must store keys digitally, use an encrypted vault and keep a hardware backup.
Also: be cautious with «connect» prompts on unfamiliar sites. Short and direct—ask why they need the connection. Don’t approve signatures blindly. If a site asks you to sign non-transaction messages, pause. My gut says a lot of these message-signing flows are attempts to authorize actions outside normal token transfers; they deserve scrutiny. On balance, most legitimate dApps will explain clearly why a signature is needed.
Common questions folks actually ask
Is a browser extension wallet safe for holding high-value NFTs?
Short answer: not ideal. Use a hardware wallet or a secured multisig for things you can’t afford to lose. Medium answer: browser extensions are fine for everyday use, small trades, and quick mints, but put the crown jewels in a safer place. I do both—fast moves in extension, long-term storage offline.
How do I check if an extension is the real Phantom (or similar)?
Start on the project’s official channels and follow links to the store. Check the publisher ID and reviews, and scan for audit reports. If the extension is open-source, compare the store build with the release artifact on GitHub; mismatches are a red flag. If you see aggressive permission requests, walk away.
Más sobre el autor
Elena Casas
